Identify vulnerabilities such as where an application may have a cryptographic algorithm vulnerability and recommend if patches or workarounds are available.
File integrity monitoring windows free.
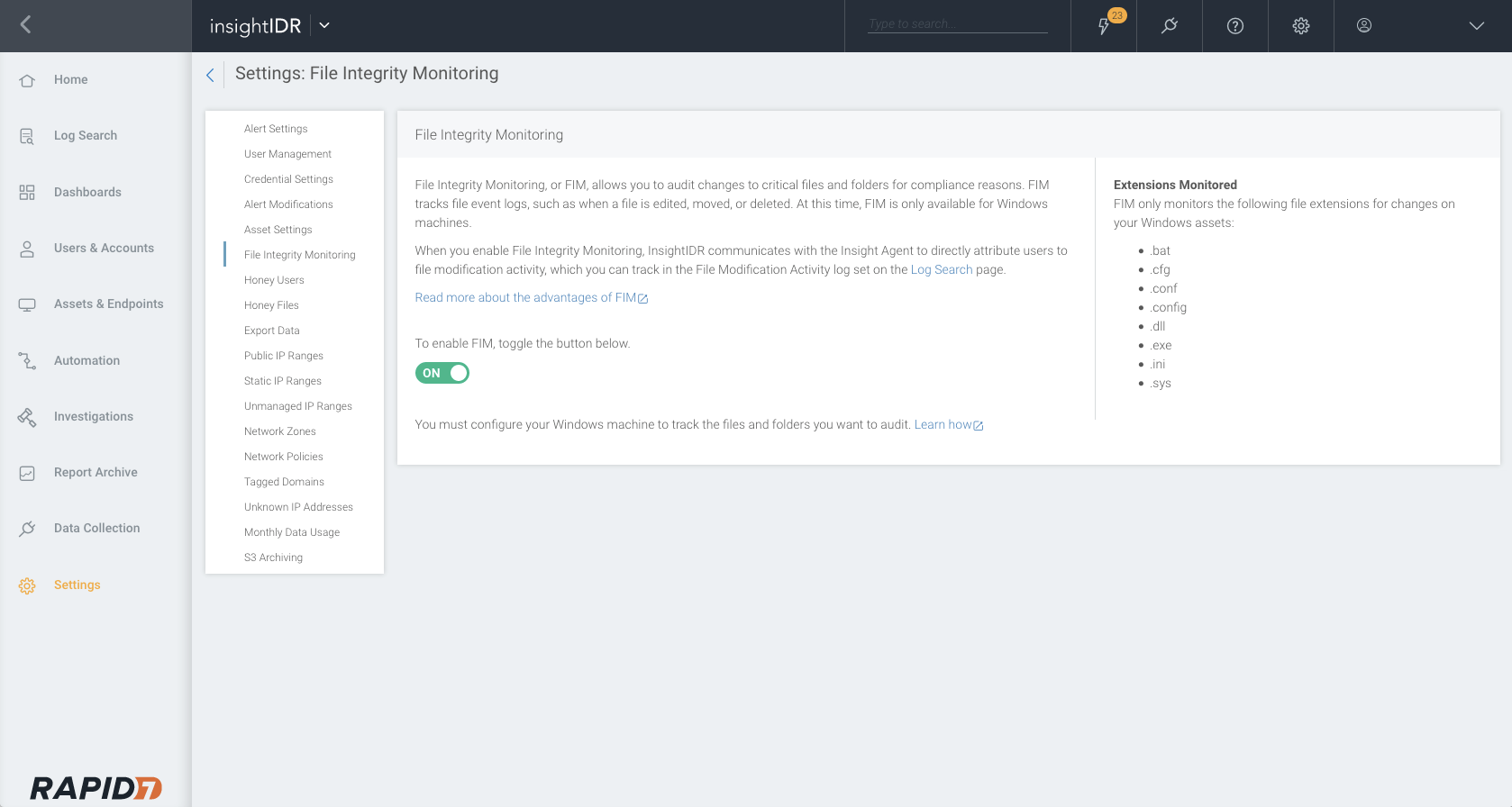
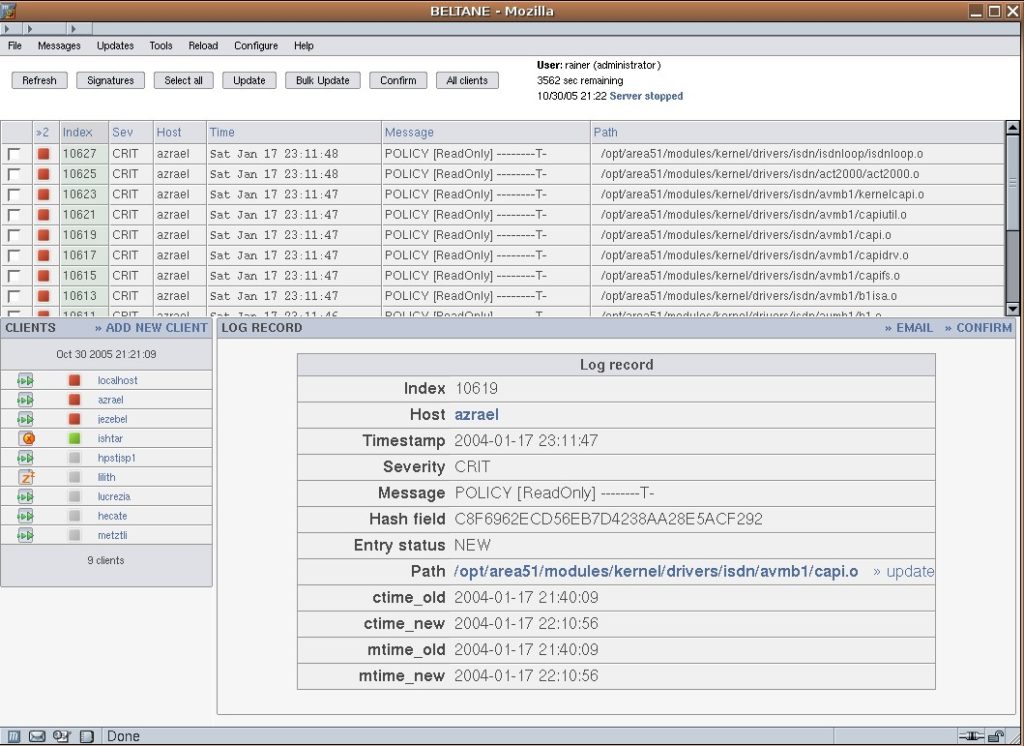
A file integrity checker calculates a hash value usually md5 or sha 1 of.
File integrity monitoring fim also known as change monitoring examines files and registries of operating system application software and others for changes that might indicate an attack.
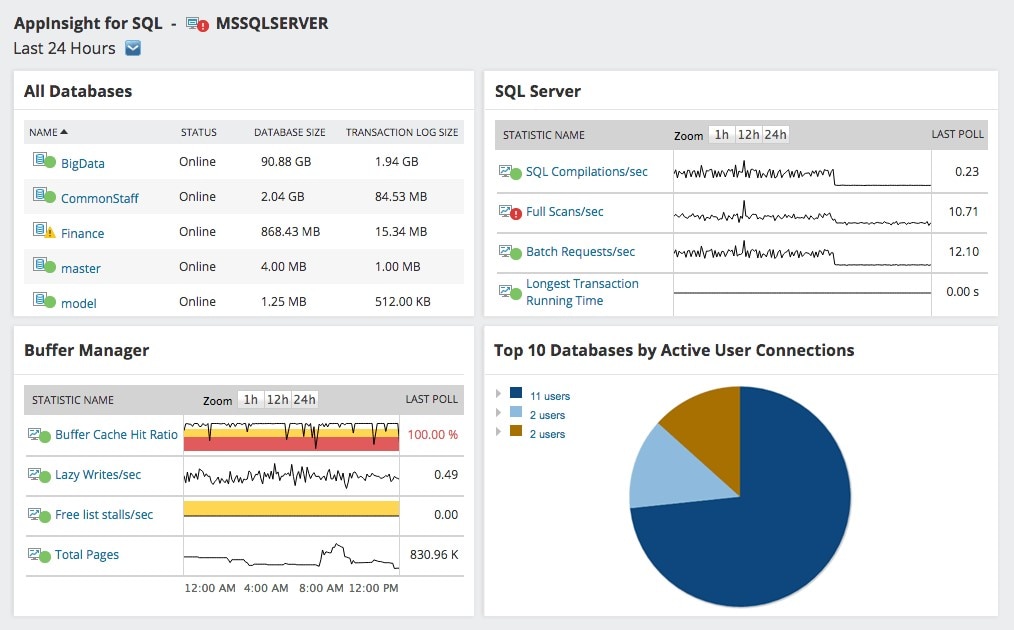
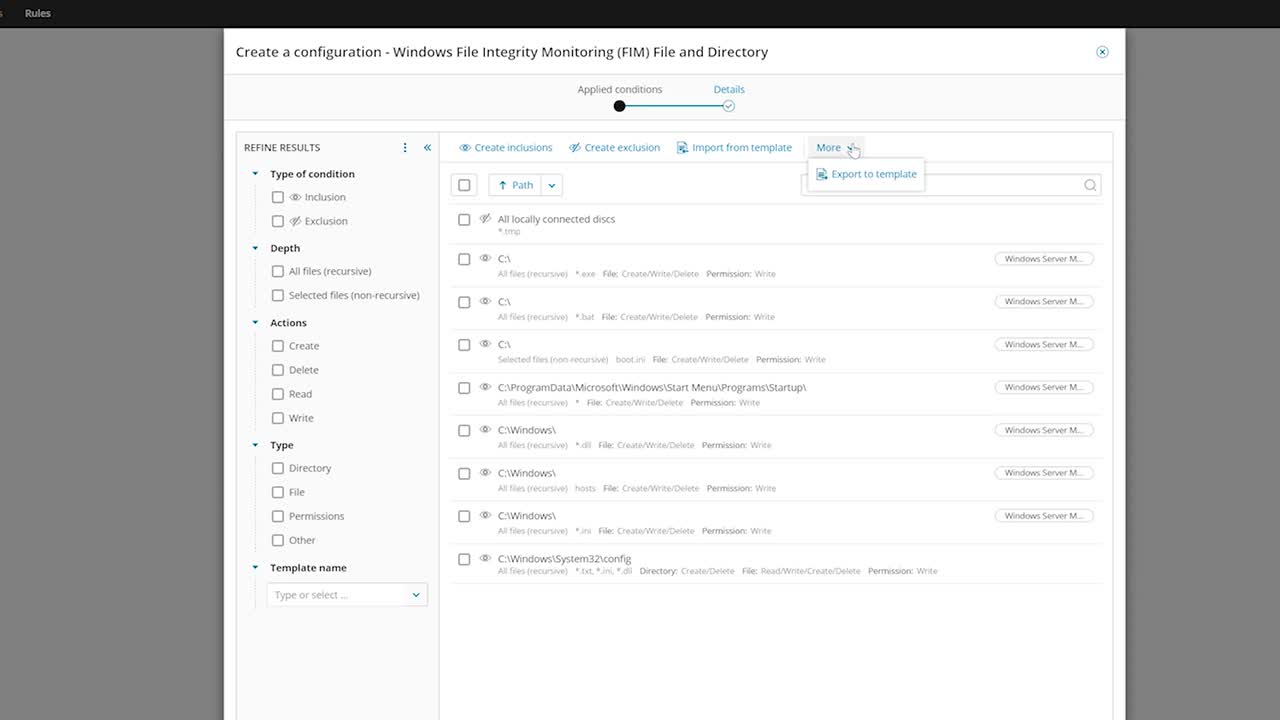
Implement change tracking and file integrity monitoring for windows iaas vms.
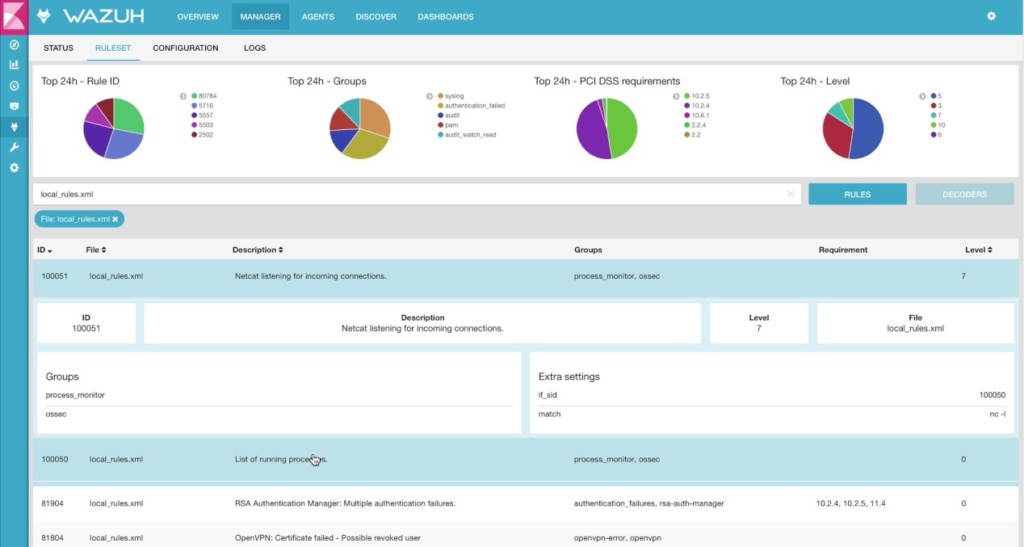
Open source tripwire file integrity monitoring tool provides security and data integrity tool useful for monitoring and alerting on specific file change on a range of systems.
File integrity monitoring software.
With continuous file access monitoring and automated incident response adaudit plus a file integrity monitoring tool is your organization s best defense against internal and external threats to data security and integrity.
The tripwire also provides the premium file integrity monitoring solution with some extra and premium features as compared to the free one.
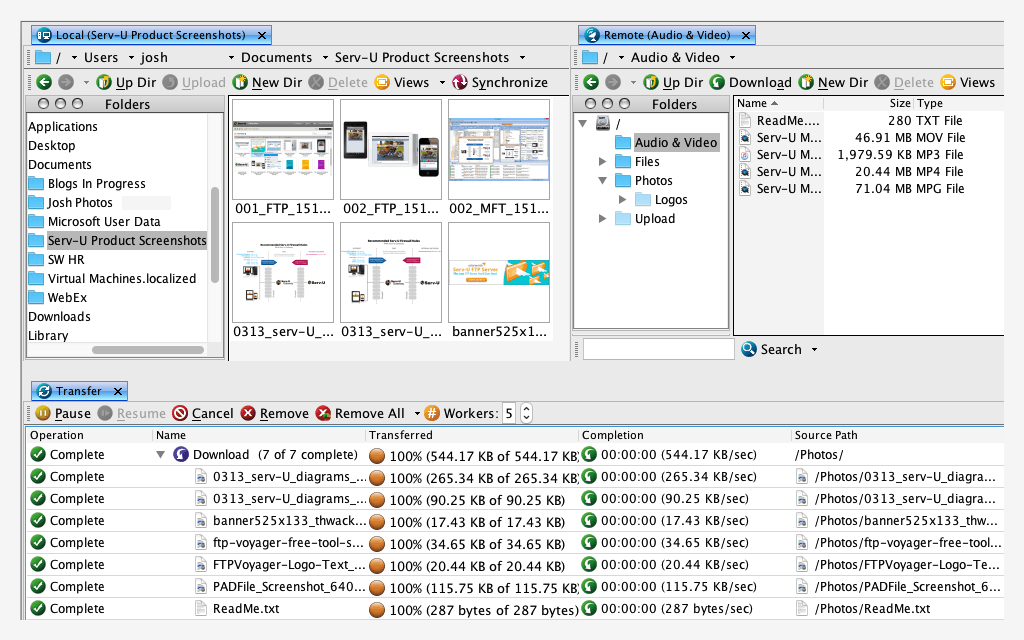
File integrity monitoring free download file checksum integrity verifier microsoft money 2000 business and personal patch.
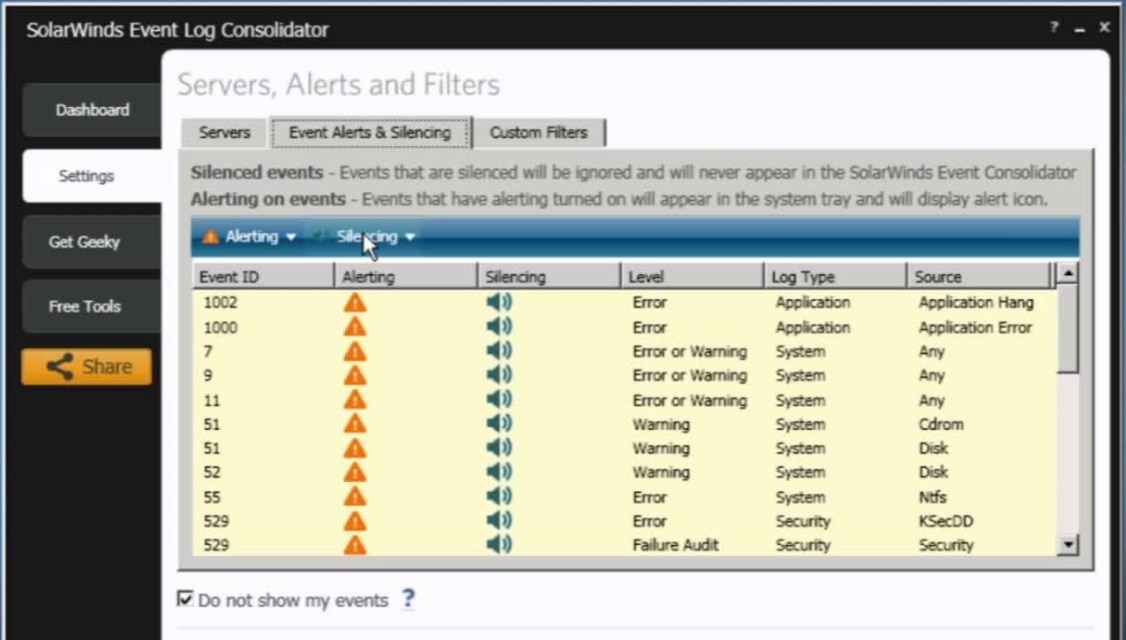
Using sem you can easily correlate system active directory and file audit events to obtain information on which user was responsible for accessing and changing a file and identify other users activities occurring before and after.
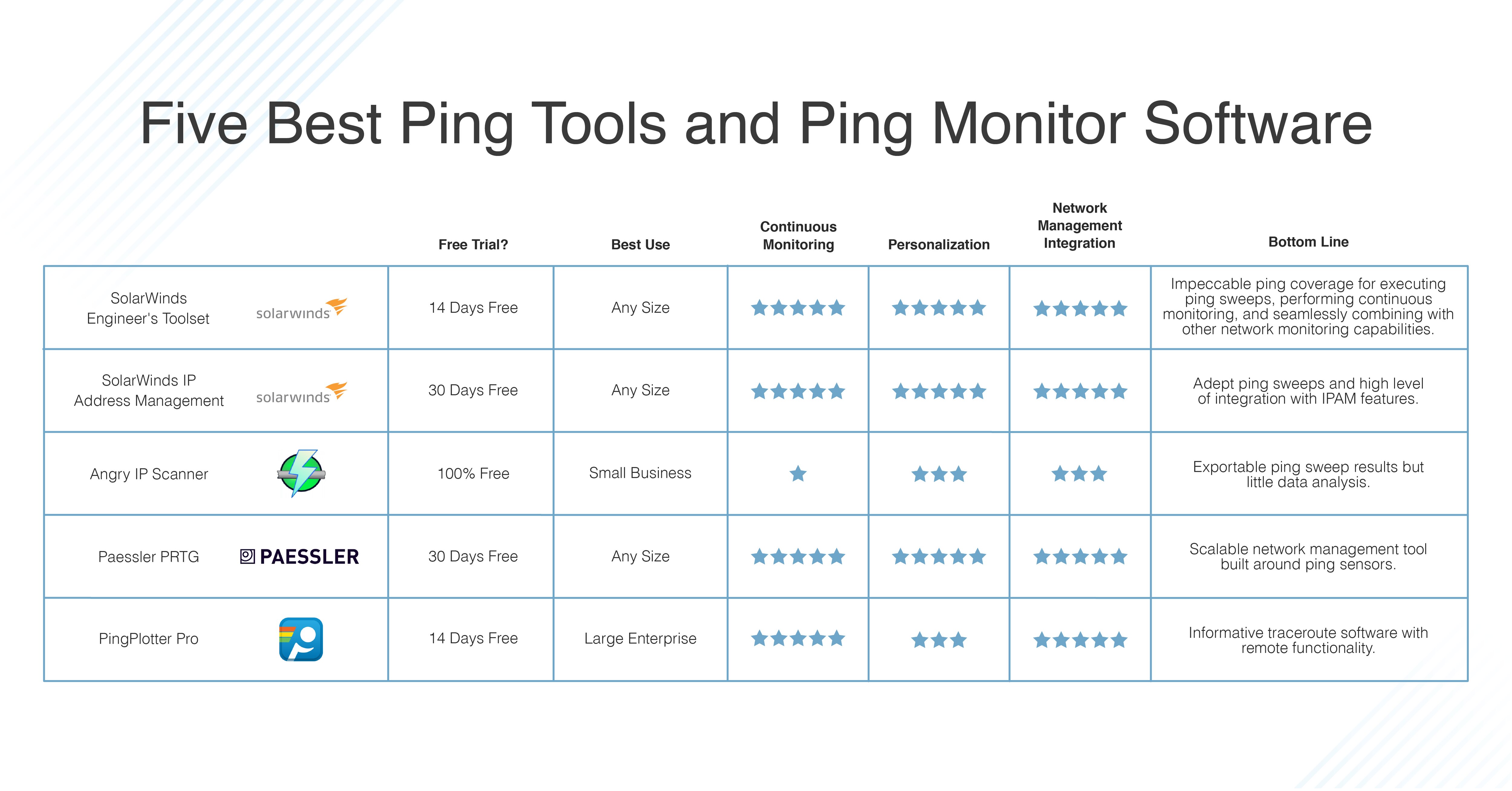
Top file integrity monitoring software comparison security event manager.
In addition the product also performs rootkit detection port monitoring detection of rogue suid executables and hidden processes.
Samhain is a free host intrusion detection system which provides file integrity checking and log file monitoring analysis.
File integrity monitoring can detect changes and access to critical system and application files and windows registry entries.
Low level file integrity check microsoft money 99 patch.
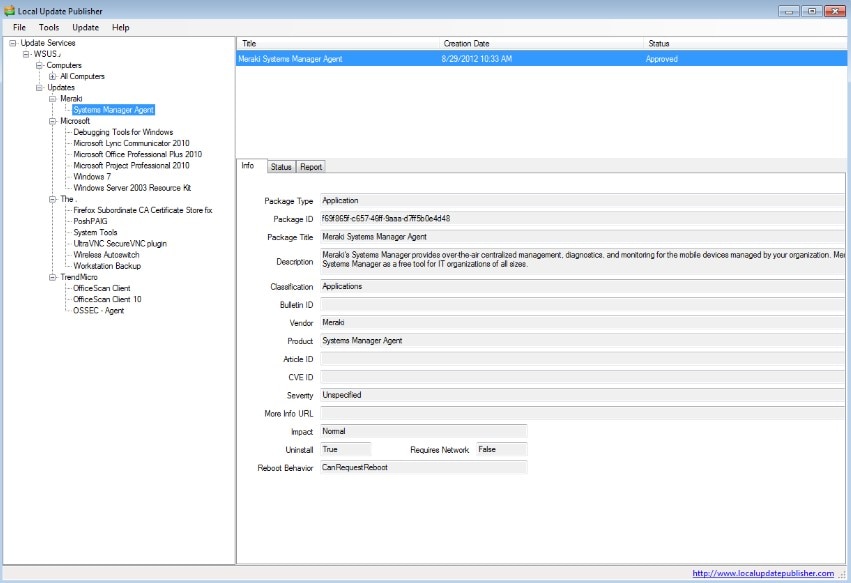
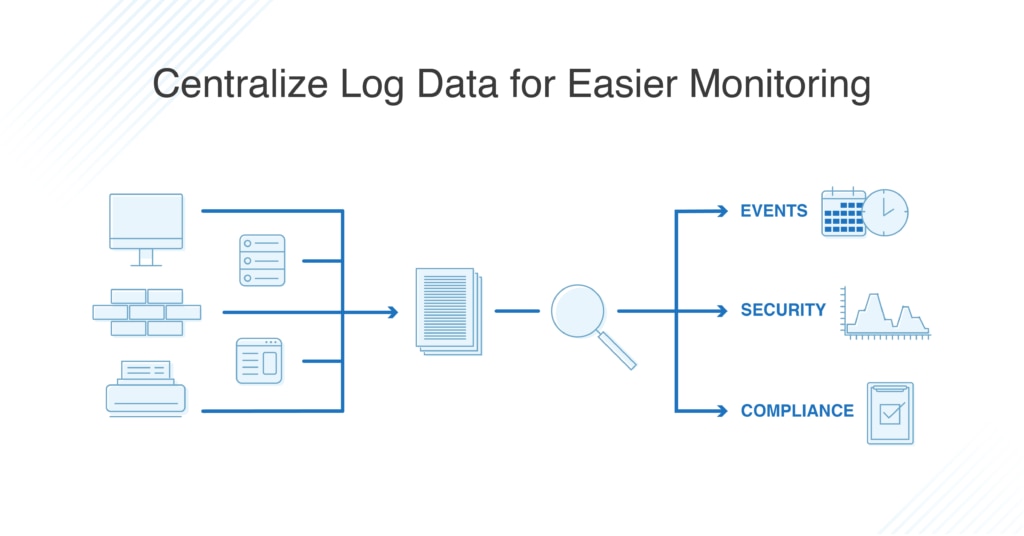
Solarwinds security event manager is a business ready option that centralizes all the information you need for effective file integrity monitoring plus other crucial monitoring tasks.
The best way to learn how to detect hacking and monitor system files for tampering is with a file integrity checker.
A comparison method is used to determine if the current state of the file is different from the last scan of the file.